The Ithaca College Office of Digital Instruction and Information Services has fielded a relatively unsophisticated phishing scam that resulted in the largest number of compromised email accounts it has seen.
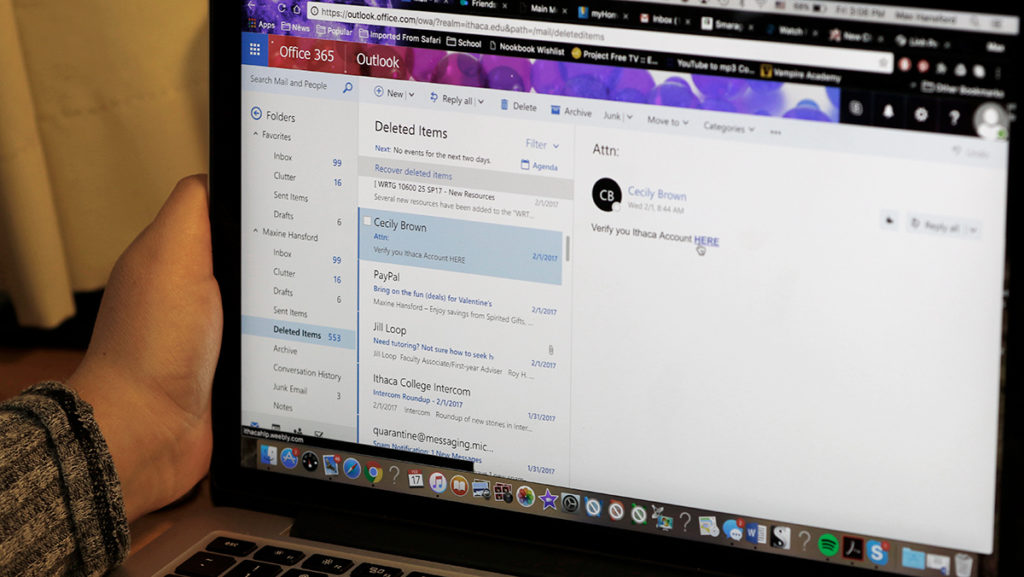
On Feb. 1, DIIS received forwarded emails from students and faculty that looked suspicious, asking users to verify their accounts by clicking a link.
The suspicious nature of these emails prompted DIIS to send an Intercom alert about email phishing to warn users at the college about suspicious emails. DIIS then used the campus firewall to block traffic to the website to which the link in the suspicious emails directed users. Phishing emails try to steal passwords and other sensitive information from users, such as credit card and social security numbers, by fooling people into providing their information.
Jason Youngers, director and information security officer for DIIS, said that after taking these precautions, DIIS received alerts from Microsoft on Feb. 2 that nine college accounts — and then Feb. 7 that five more college accounts — were sending spam from their Office365 email accounts. DIIS then changed the passwords on these accounts and contacted each account holder to reset their passwords.
The email that was sent out to college users stated in the body of the email, “Verify you Ithaca Account HERE.” Mark Maunder, chief executive officer at Wordfence, a website that specializes in cyber security, said the spelling error in the email provides some clue as to who sent the emails.
“I think that the only thing that indicates is that it’s someone who’s not a native English speaker,” Maunder said. “That’s the only thing you can reliably tell from that.”
Youngers said the Microsoft notification’s proximity to the phishing emails probably was not a coincidence and the accounts that were sending spam were doing so as a result of the users’ falling for the phishing email.
“Because of the timing, it seems most likely that these email accounts were compromised in the phishing attack,” Youngers said. “Of the 14 accounts, 12 were students, one was a retiree, and one was an IC affiliate.”
Youngers said that while this number of phishing emails has occurred before, the number of compromised accounts has not.
“We have occasionally had email accounts compromised and used to send spam, but I am not aware of a cluster this large,” Youngers said.
He said he is not aware of where these emails originated from and does not believe that any information was taken besides the now-changed email account passwords. He also said he does not know for certain where the attacker obtained the email accounts.
Maunder said for this phishing attack, a reason for the emails could be for monetary gain, and some email accounts are more susceptible than others.
“It might be as simple as there’s some financial incentive for them where, if they can compromise the accounts they go after, they can access a student loan system that allows them to transfer funds,” Maunder said. “Any service where you don’t have two-factor authentication enabled, they would be able to compromise that by having access to your email accounts.”
Freshman Matias Weilmann said he received one of these emails and didn’t open it because it looked suspicious. However, just receiving the email was not what worried him the most.
“I’m wondering how they got my address in the first place,” Weilmann said.